How to do practical wireless hacking
Nowadays, there are wireless hotspots everywhere! You can get internet access with a wireless enabled laptop almost everywhere you go. so it's easy and manageable wireless hacking. In this chapter I will discuss ways a hacker goes about getting into secure wireless networks and things he can do once he is inside.
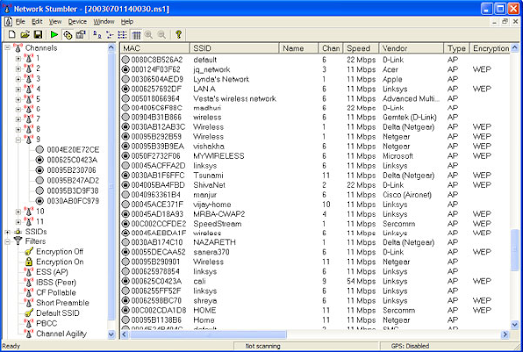
Scanning for Wireless Networks for wireless hacking
For this section and the following, you will need to have a wireless card/adapter. The hacker starts by scanning for wireless networks near him. The Windows tool we will use in this section is called NetStumbler. Also by this time MacStumbler may already be released for those of you using a Mac. Some other similar programs are:
• Kismet for Windows and Linux.
• KisMac for the Mac.
1. Download and install NetStumbler.
2. Run it. It automatically starts to scan for wireless access points.
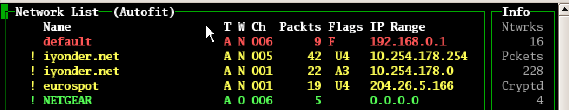
3. Once it is completed, you should see a list of all the wireless access points around you.
4. If you click on the MAC address of one of the discovered wireless networks under channels, you will see a graph that shows the wireless network’s signal strength. The more green and the less spaces, the better the signal.
5. As you can see NetStumbler provides a lot more than just the name (SSID) of the wireless network. It provides the MAC address, Channel number, encryption type, and a bunch more. All of these come in use when a hacker decides he wants to get in the secured network by cracking the encryption. The most common types of encryption are:
• WEP (Wired Equivalent Privacy) – WEP isn’t considered safe anymore. Many flaws have been discovered that allow a hacker to crack a WEP key easily.
• WAP (Wireless Application Protocol) – WAP is the currently the most secure and best option to secure your wireless network. It’s not as easily cracked as WEP because the only way to retrieve a WAP key is to use a brute-force or dictionary attack. If your key is secure enough, a dictionary attack won’t work and it could take decades to crack it if you brute-force it. This is why most hackers don’t even bother.
Cracking WEP
In this command, the -3 tells the program the specific type of attack which in this case is packet injection, -b is the MAC address of the target access point, -h is your wireless adapters MAC address, and the wireless adapter device name goes at the end.
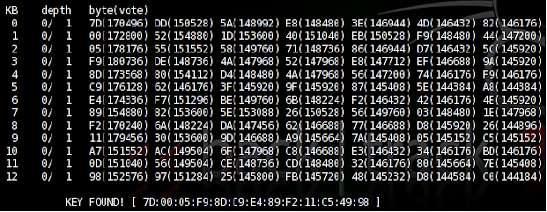
8. Once you have collected around 50k-500k packets, you may begin the attempt to break the WEP key. The command to begin the cracking process is:
aircrack-ng -a 1 -b [bssid] -n 128 [filename].ivs
In this command the -a 1 forces the program into the WEP attack mode, the -b is the targets MAC address, and the -n 128 tells the program the WEP key length. If you don’t know the -n , then leave it out. This should crack the WEP key within seconds. The more packets you capture, the bigger chance you have of cracking the WEP key.
With all the different computers and network adapters out there, you may come across a error occasionally. If you get stuck, remember, Google is your friend! Search for an answer and I guarantee you that 99% of the time you will find a solution.
With all the different computers and network adapters out there, you may come across a error occasionally. If you get stuck, remember, Google is your friend! Search for an answer and I guarantee you that 99% of the time you will find a solution.
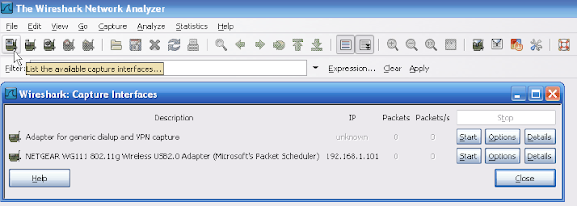
Packet Sniffing
5. Now to show you an example of how Wireshark can be used I will start up Windows Live and send a message. As you will see in the image below, my whole conversation will be captured. To filter out all the useless data and to only display the Windows Live related packets type in “msnms” in the filter bar.
6. As you can see, my message is displayed at the bottom. If I continue down the list I can see the whole conversation. Usernames and passwords are captured the same way, and if they aren’t encrypted, you can see them in plain text.
Some other useful sniffing programs to learn:
• WinDump
• Snort
• Dsniff
Countermeasures
There are a few countermeasures you could follow to keep your wireless network safe from hackers.
1. Change your routers default password and make sure you have WAP encryption enabled. If your router doesn’t have a WAP option, use WEP. It is better than nothing.
2. Use a long secure password for your router. Include numbers, lowercase letters, uppercase letters and other symbols. The more obscure the better.
3. Make sure your router has the option to not broadcast your SSID enabled. This will prevent some programs like Net Stumbler from locating your wireless network.
4. Use MAC filtering on your router. Every wireless card and wireless adapter has a MAC address. By choosing to allow only your MAC addresses onto the network, you can keep a lot of attackers out.
5. To prevent packet sniffing attacks from affecting you, make sure the important sites you use, like banks, use SSL (Secure Socket Layer) encryption. You can tell if the site has SSL enabled if the URL begins with https:// instead of http:/.
6. In cafés or other hotspots where internet is free, packet sniffing is very common. To avoid being affected use a VPN (Virtual Private Network) service to encrypt the data you send across the internet.








Comments
Post a Comment